Author – Yeremia Sion Chrisdianto, NetApp Presales Mega Buana Teknologi
Ransomware attacks have spread rapidly across the globe, including Indonesia. This type of malware is particularly dangerous because it can cause major operational disruption and financial damage for organizations that become victims. Ransomware is a form of malicious software that infiltrates computer systems, especially those running Windows operating systems, and encrypts critical files so users can no longer access their own data.
The Indonesian Ministry of Communication and Information Technology (KOMINFO) has warned organizations and the public to take proactive steps to prevent malware attacks, especially ransomware variants such as WannaCry.
In Indonesia, ransomware has already affected several hospitals and institutions. These attacks typically begin when malware infiltrates a Windows system and replicates itself within system files. Once inside, it can encrypt files within minutes or even seconds. After the files are locked, attackers display a message explaining how victims can regain access by paying a ransom, usually through Bitcoin. If the ransom is not paid within the specified timeframe, the data may be permanently deleted.
To protect enterprise data and sensitive customer information, organizations need a layered security strategy that goes beyond traditional perimeter defenses. Many companies focus on stopping attacks from entering the network, but critical business data often resides deeper within the storage infrastructure that attackers ultimately target. NetApp helps organizations strengthen protection at the storage level while improving how enterprise data is managed. With NetApp ONTAP, organizations gain powerful capabilities that enhance efficiency while helping safeguard their most valuable digital assets.
1. Point-in-Time Data Protection
Creating point-in-time, read-only copies of enterprise data at regular intervals such as hourly, daily, or weekly allows organizations to quickly restore files from a specific moment without paying ransom to attackers.
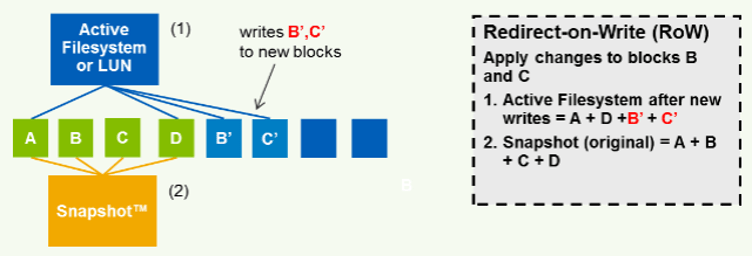
With NetApp Snapshot technology, data remains exactly as it was when the snapshot was taken. Because the snapshot copy is read-only, it cannot be modified or encrypted by attackers. If an organization experiences a ransomware attack, attackers can only encrypt files that were created after the most recent snapshot. By maintaining regular snapshots, organizations can simply restore their systems to the latest safe version and avoid paying ransom.
Another advantage is that snapshots do not consume large amounts of storage. NetApp Snapshot uses Redirect-on-Write (ROW) technology, which stores only the changed data blocks instead of creating full copies of entire volumes. This approach saves storage space while allowing organizations to restore even terabytes of data within seconds.
2. Snapshot Retention Strategy
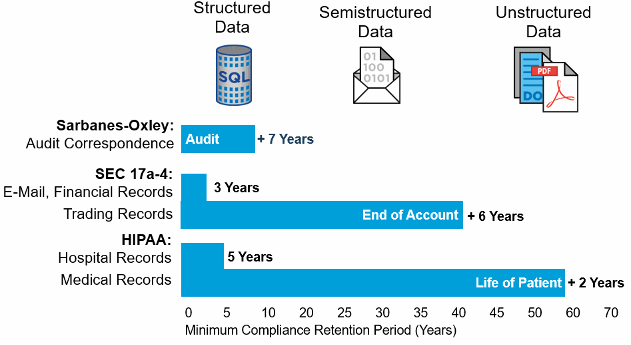
Technology is only as effective as the policies that govern it. Implementing a well-designed storage retention policy ensures that organizations keep enough historical data copies for reliable recovery.
Some ransomware variants remain dormant for months before activating. Because of this behavior, organizations are advised to retain snapshots for several months. If an attack occurs later, they can still recover clean versions of their data from earlier snapshots.
By maintaining long-term snapshot retention, organizations strengthen their ability to recover from delayed ransomware infections.
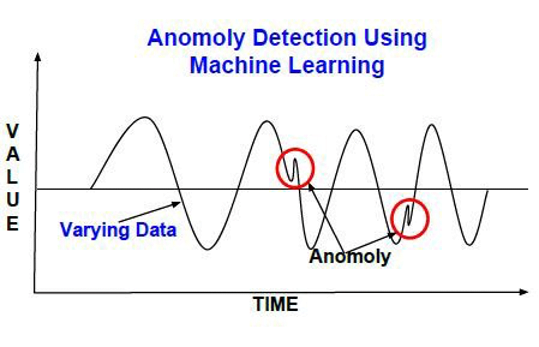
3. Detecting Data Anomalies
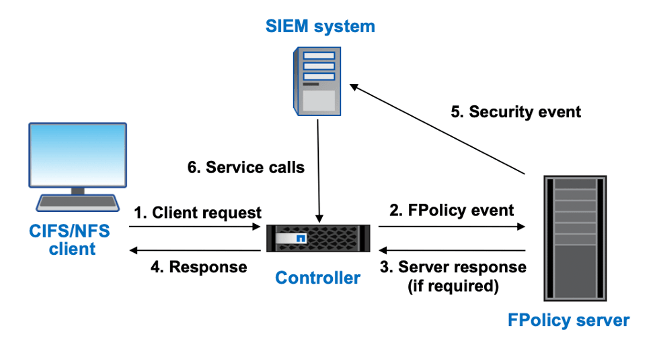
Organizations often implement internal policies regarding how employees store and manage company data. NetApp FPolicy helps strengthen ransomware protection by monitoring data behavior directly at the storage level.
FPolicy operates using a zero-trust model and integrates with Access Control Lists (ACL) to enforce permissions. Combined with AI and machine learning technologies, it can analyze user activity through User Behavior Analytics (UBA).
By learning normal user behavior patterns, FPolicy can identify anomalies or suspicious actions. If a user attempts to store unusual or abnormal data, whether intentionally or accidentally, the system can automatically deny access and send alerts to administrators for further investigation.
4. Filtering Suspicious File Types
Originally designed to prevent unwanted files from being stored within enterprise storage infrastructure, NetApp FPolicy can also monitor, filter, or block file traffic based on file extensions and metadata. Through file access notification mechanisms, organizations gain visibility into file activity and can enforce policies that restrict suspicious file types.
For example, when users attempt to download attachments or files such as suspicious images or other potentially harmful formats, the system can block those files from entering the organization’s database environment.
This capability helps reduce the risk of malware entering the enterprise storage environment through infected files.
5. Locking Data with Immutable Storage
While snapshots can prevent automatic deletion of data, human error can still create problems. In some cases, internal users may unintentionally modify or delete important data before the organization realizes what has happened. NetApp SnapLock addresses this risk using a Write Once, Read Many (WORM) approach. With SnapLock, snapshot copies cannot be modified, renamed, or deleted once they are committed according to configured policies.
After data is locked in this immutable state, it remains protected within the storage system for the defined retention period. This ensures that critical enterprise data cannot be altered or removed, even by administrators or malicious actors.
By implementing immutable storage controls, organizations can significantly strengthen their defense against ransomware and data tampering.